SSH: Difference between revisions
Brian Wilson (talk | contribs) |
Brian Wilson (talk | contribs) |
||
| Line 83: | Line 83: | ||
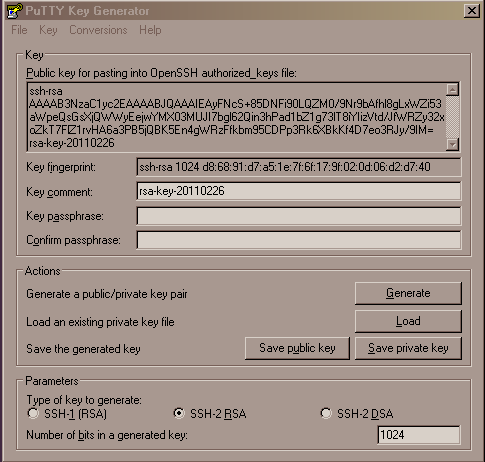
Download the PuttyGen tool from the [http://www.chiark.greenend.org.uk/~sgtatham/putty/ Putty site]. Run it and click the "Generate" button to generate a key pair. Enter a passphrase to protect the private key. | Download the PuttyGen tool from the [http://www.chiark.greenend.org.uk/~sgtatham/putty/ Putty site]. Run it and click the "Generate" button to generate a key pair. Enter a passphrase to protect the private key. | ||
'''Remember to save both keys!''' | |||
Send the public key to me, you can just cut and paste it into an email from the window. Here is a screen shot. | Send the public key to me, you can just cut and paste it into an email from the window. Here is a screen shot. | ||
Revision as of 01:06, 27 February 2011
What is SSH for?
SSH allows two computers to exchange data securely over unsecure links (for example, the Internet).
The server can encrypt data using the public key that you will give me. Only you (with your matching private key) can decrypt the data that my server sends you.
To set this up, you have to generate a pair of ssh keys and send me your public key.
More information on ssh can be found at http://www.openssh.org/
Why use SSH?
It's secure
The entire session is encrypted. This means you can work in a cafe over wifi and not worry about anyone snooping. Note that you DO have to use a computer with ssh installed on it and have a copy of your private key on it.
Many tools support it
Any tool that supports ssh or sftp can talk to the server.
For example, on Ubuntu (and other Linux computers that use Nautilus file manager) you click "Places"->"Connect to Server..." and you can open a file manager window and drag and drop files between your computer and my server.
Many people like to use the free Filezilla program to transfer and synchronize files. It runs on Linux, Mac, and Windows. Non-free commercial tools such as Dreamweaver and ActiveState Komodo have support built in to allow opening, editing and saving files directly on the server via sftp.
The URL to access HuPI.org web server via SFTP is sftp://hupi.org/var/www/hupi.org/ -- you can use this in Filezilla as the host name. Use your username and leave the password blank.
Of course command line tools work too (sftp, scp, ssh, rsync).
Filezilla for Windows
Using ssh shared keys with Windows requires a little more work than Linux or Mac.
Filezilla on Windows depends on installing the Putty tools. You will need Pageant and PuttyGen.
Additional Filezilla instructions are here: http://wiki.filezilla-project.org/Howto
Putty is also useful for accessing the server via command shell.
Another popular Windows tool is WinSCP.
Why use SSH key pairs?
We never have to exchange any secrets: I don't need to give you a password. We don't have to send secrets through email. I will never know what your password is since there isn't one. Only a passphrase to protect your private key.
When you connect to my server, all data transmitted over the networks is encrypted. This means you can safely work in any public places or use wireless connections without worrying who is sneaking a look at your traffic.
\* Strictly speaking you don't need to use a passphrase, but if you put the key pair on a portable computer it protects us both if the computer is lost or stolen. No passphrase means you don't have to type your passphrase to connect to my server.
Case 1. You want access to a server that I manage (HuPI.org)
Linux and possibly Mac users
- If you already have an ssh key pair then you only need send me your public key.
- If you don't have a key pair, you will need to generate a new pair.
On Linux or Mac, the ssh files live in your home directory in the hidden folder called .ssh (That's a dot followed by ssh)
If you don't have a folder called .ssh then you don't have keys either. Here are all the commands to create the folder and generate a key pair.
# move to your home directory cd # create the folder mkdir .ssh # protect the folder chmod 700 .ssh # generate keys, use a passphrase you can remember # this will overwrite existing keys, you might not want to do that! ssh-keygen
This will create the files id_rsa and id_rsa.pub in .ssh by default, you can specify a zillion things other on the command line such as a different name for the files like maybe 'id_rsa_hupi'
Now send me just the file id_rsa.pub in an email. (It's in your .ssh folder.)
Special notes for Macintosh
The next time I sit at my Mac I will fill in this section.
Windows
You could install Cygwin and just follow the Linux instructions, but I am assuming that you use Windows because you don't like command lines.
Download the PuttyGen tool from the Putty site. Run it and click the "Generate" button to generate a key pair. Enter a passphrase to protect the private key.
Remember to save both keys!
Send the public key to me, you can just cut and paste it into an email from the window. Here is a screen shot.
Case 2. Granting me access to your server
This section explains the case when you want me to do some work for you and you need to give me access to your server(s).
- You have to run an sshd server on your machine.
- I send you my public key.
- You add my key to the accounts that you want to allow me to have access to. For example, you can create a personal account for me with the username "bwilson" and add the file in /home/bwilson/.ssh/authorized_keys and optionally also put a copy in /root/.ssh/authorized_keys to give me root level access.
Then I can use an ssh client to connect. I enter my passphrase and the client uses the decrypted private key to authenticate with your system. If the private and public keys match, your system grants me access.
As long as I don't share my passphrase with anyone, even if I lose my laptop, no one can use my private key to access your machine.
If you want to revoke access, you remove or disable access to my public key(s).
You don't have to give me any password information on your machine, so you don't have to change the root password when we are done working together.
This is what an RSA public key looks like
ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEAsfKX946JbxemrYTT55dTk9Bg98tLeH3PAi5/cpQkWdntATz4ISIvqOltXkKrssj3dlK57M5u86RA05mzIOLPel9o52WCiYUdGiCnAOJa7fS9+XBU2rtrsgl0NBttVbC/m1qH1Ff6WKcGEwjlwxZvQAMk6pdSLDf9A4bns1qpS+jdD4nBOsVjx9cF6MD+1dHd/JqpNfllXDLeFsNNBivQ8ansAMiOj4WwXyU+XgbaZGngl1LYuwc1Lk+5N8Z4wq+33ERokvKOvNl8dAe4/n0oZqMF7LU+rHqIpUiusDRryFF+O2ogb+yTCwz0TYxNwg0tkTFFZN4xqc5hjhFgWrCuOvPQ== [email protected]
Key file installation notes
This is how to install a public key on a server.
The "authorized_keys" files are text files containing public keys. You can add new keys from the command line or use a text editor. The ownership and permissions should be set to be owned by the user account and readable only by that user. The typical commands:
# cd /home/username/.ssh move to user's directory # cat /tmp/id_rsa.pub >> authorized_keys append key to file # chown username authorized_keys fix ownership # chmod 600 authorized_keys fix permissions